Scam Alert: Remote Access Scams
Mar 11 2026

Mar 10 2026
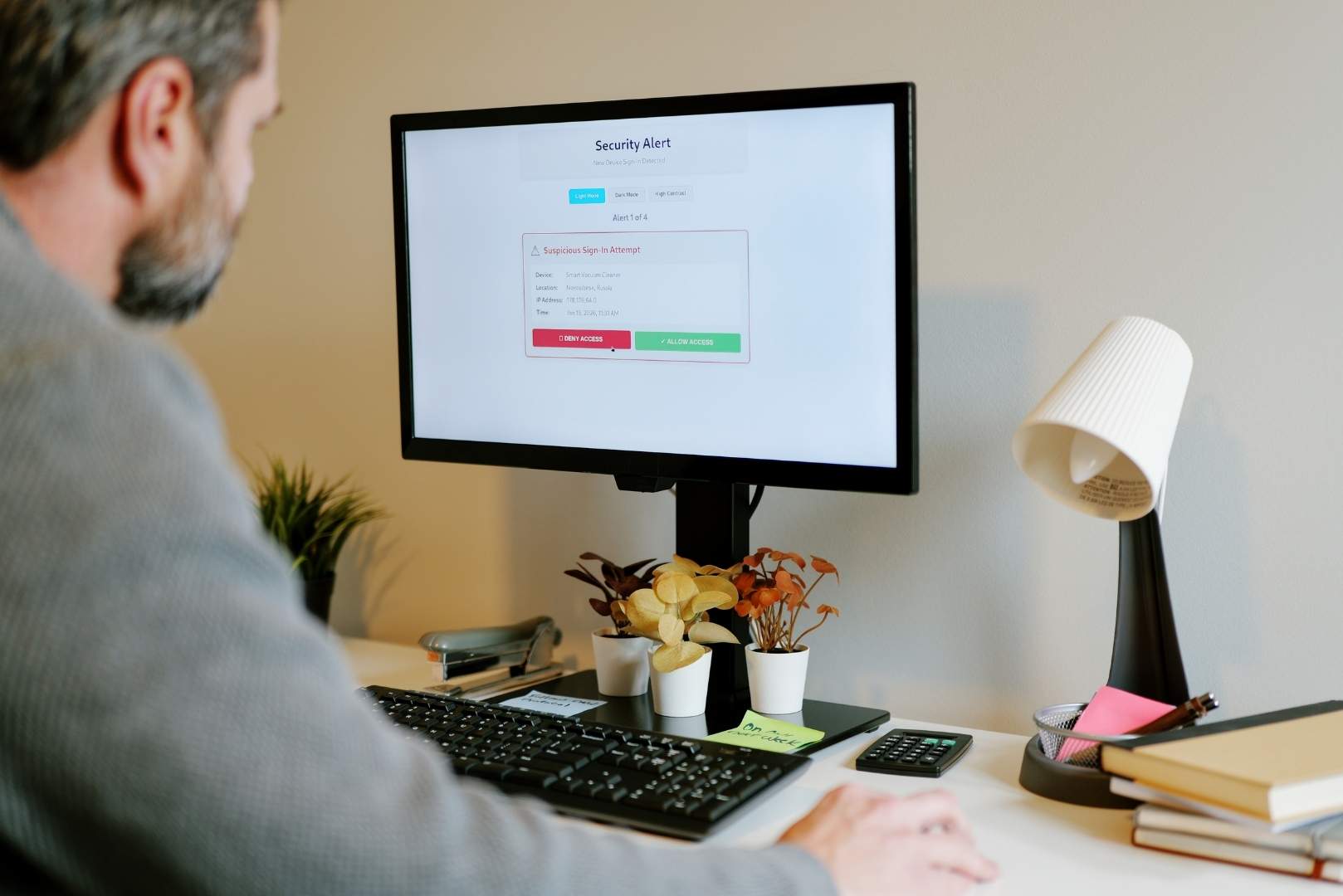
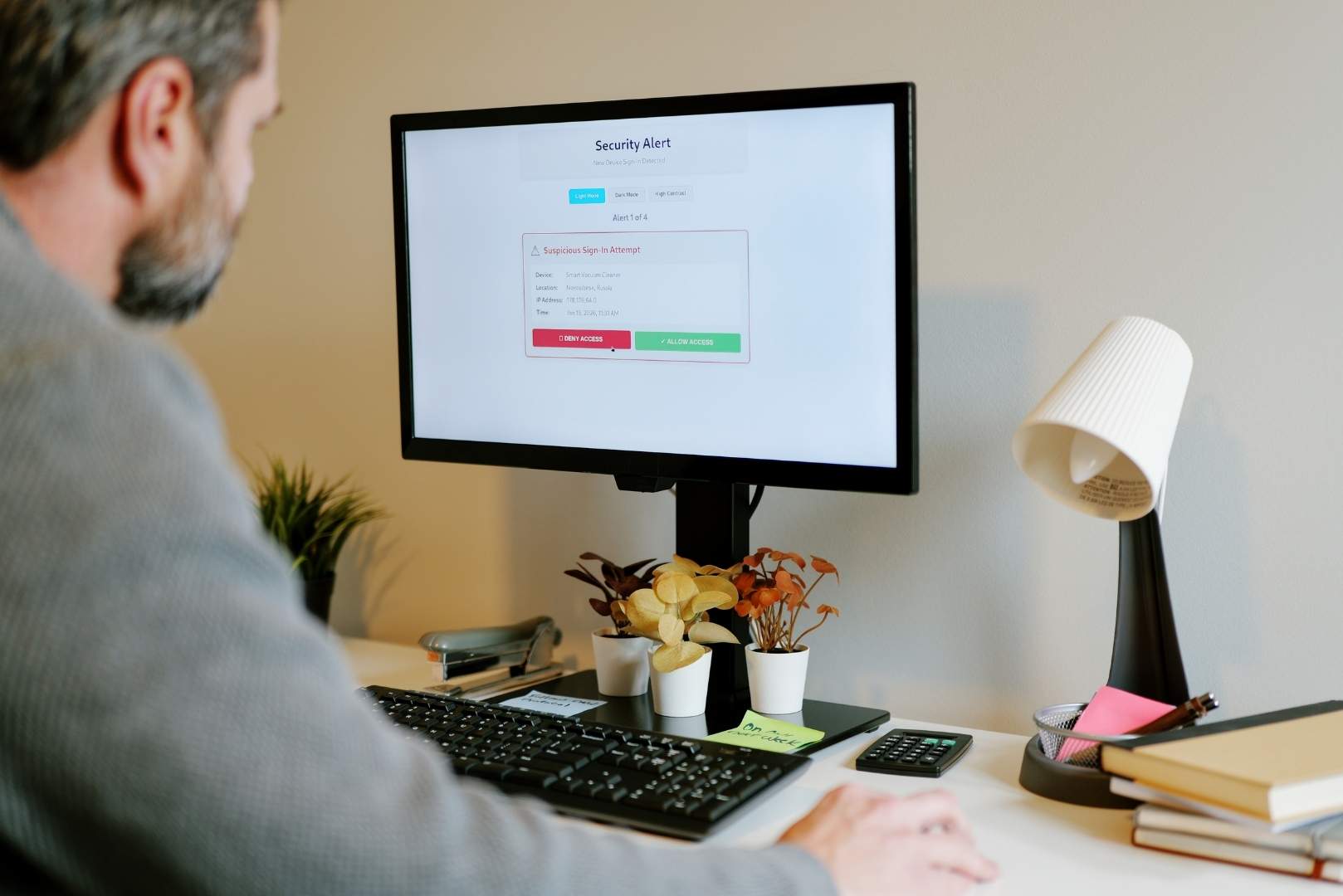
Scanning a Quick Response (QR) code to access a website or make a payment is becoming more common, and scammers are using this trend to trick victims into accessing malicious websites and sharing sensitive financial information. Here are a few things to think about before scanning a QR code:
If you think you’ve fallen victim to a QR code scam like the one below, contact your local branch or our Customer Care Center at 888-816-8064 for assistance.
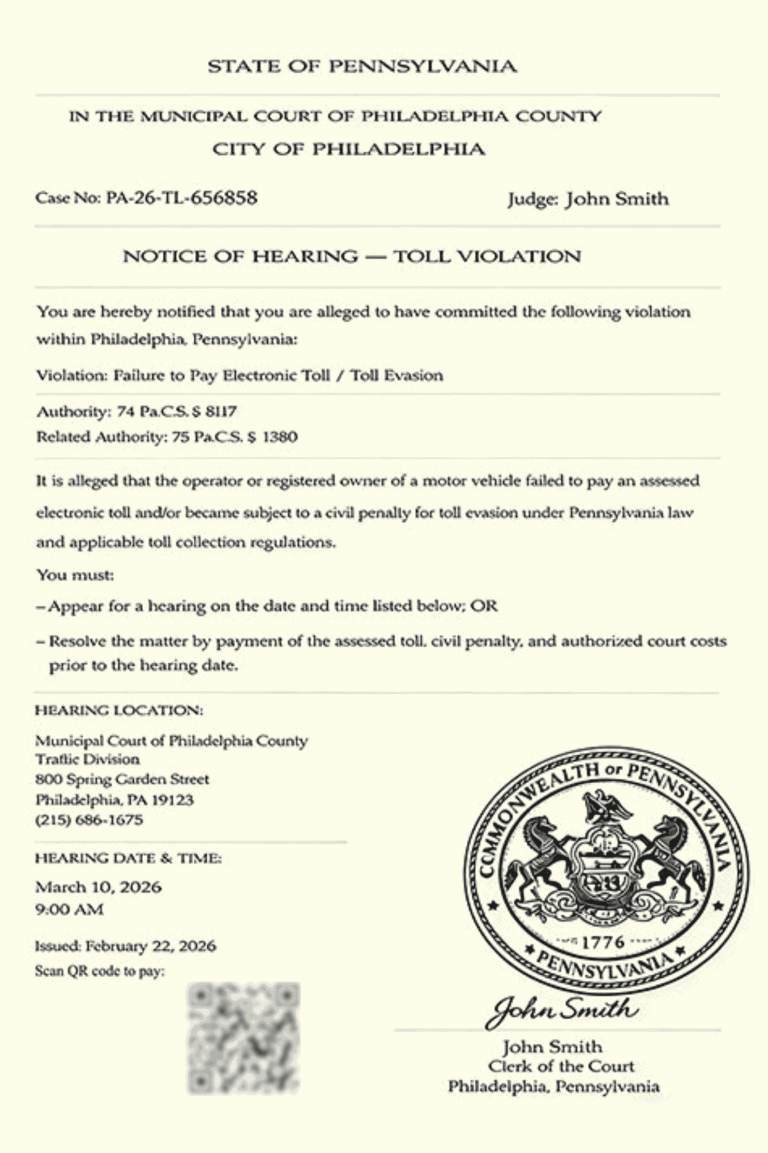
How it works:
Mar 11 2026

Feb 09 2026